Internet of things: security concerns over cheap IoT toys and gadgets
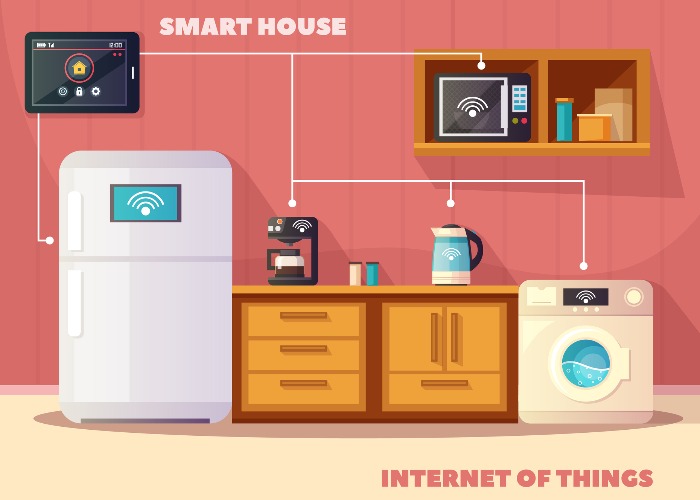
Internet of Things (IoT) gadgets have seen a sharp rise in popularity but are they safe and is there a bigger cost to buying cheap?
Internet of Things (otherwise known as IoT) devices have seen a huge rise in popularity in recent years.
In a bid to satisfy the consumer craving for convenience and connectivity, manufacturers have been aggressively adding wireless connectivity to their entire product line.
We're living in a world where fridges come with WiFi, cars with Twitter and toothbrushes with Bluetooth are widely available.
Whenever a big name manufacturer releases a new "smart" or "connected" product, researchers like myself are drawn to investigating the potential security and privacy issues that device may have.
For the most part, these manufacturers are pretty good at responding to any concerns and fixing issues fairly quickly.
For the smaller "pop-up" manufacturers though, it's a slightly different story.

Attack of the clones
Copycat or "off-brand" products are certainly nothing new and, unsurprisingly, are incredibly popular thanks to various online shopping sites allowing manufacturers from abroad to sell directly to consumers for a fraction of the price of the legitimate version.
Often, we justify their purchase by telling ourselves that a shorter product life, or any potential hassle with the product, is a decent trade-off for saving money.
Since technology is expensive in the first place and changes so rapidly, it can be very tempting to purchase an "off-brand" product over a big name manufacturer.
This can be a risky approach, however, especially with products that are IoT ready and the reason for this is simply down to how these products are manufactured.
Much like smaller, start-up style businesses, copycat manufacturers can disappear as quickly as they appeared – and if that product has an IoT component, it can often stop that feature working entirely or, worryingly, could be exploited by criminals to spy on you or your family.
Read more: the danger of fake electrical goods
How your IoT gadgets can be turned against you
Simplistically, many IoT devices regularly "phone home" to a central website controlled by the original manufacturer in order to function, receive updates, or pass on commands.
While this website remains in the hands of the original manufacturer, it's in their interest to maintain a stable service.
If the manufacturer that operates the control website were to go out of business or stop paying for their domain name, that website can be registered by anyone and, with a little tweaking, your IoT device can fall under their control.
While more expensive big brand IoT products may have additional security features in place to detect this type of foul play and protect the consumer, it's uncommon for a cheaper clone to contain such sophisticated measures.
Check your credit report for any suspicious financial activity
I was able to do it
A few years ago, my curiosity was piqued by a special offer for smart teddy bears that cropped up on a shopping site.
Upon clicking on the product, as it was exceptionally cheap and therefore quite enticing, I noticed that the reviews were somewhat negative with many users claiming the app to connect to the bear wasn’t working.
I decided to purchase a couple to research IoT devices further.

When they arrived, I downloaded the app from the app store as required and faced the same issue mentioned by various reviews on the product page.
Digging deeper, I noticed that the app was trying to connect to a website that wasn’t responding.
The reason it wasn’t responding was that the manufacturer had allowed the domain name to expire, freeing it up to be registered by anyone.
Upon registering the domain, it took seconds for it to suddenly get a large number of hits from the teddy bears and apps from all over the world.
Given that I now controlled the central website that the app, and teddy bears themselves, were attempting to connect to, I could theoretically control these products.
Felicity Hannah on how to stay safe by revealing as little possible online
Insecure by design
Criminals don't always need to wait on manufacturers going out of business to target your IoT gadgets though.
Due to the speed at which these cheaper products are manufactured, often the software component can be a bit of a rushed job.
Many copycat devices often ship with long out of date or custom software that is riddled with many well-known security holes.
Focusing solely on sales rather than long-term customer service, this can mean that these issues are never addressed by the manufacturer in the lifespan of the product leaving a myriad of devices vulnerable to attack.
By exploiting these vulnerabilities, criminals are able to penetrate your home network, allowing them to monitor communications or even control other smart devices connected to the same network – even if they're not vulnerable themselves.
Read more from Scott McGready on security here
Security tips for owning IoT devices
If you own an IoT device, even if it's relatively simple, don't forget to:
- Update all IoT or smart devices regularly.
- Check reviews or search online for the product's name before buying as this may bring up concerns raised by other consumers or security researchers.
- If your router has a guest network feature, connect all IoT products to it instead of the main network. This creates two networks, both with internet connectivity but insulated from each other.
- Be wary when buying "smart" devices – especially toys – that are considerably cheaper than the big brand alternatives.
- Consider buying non-smart products unless it's absolutely necessary. While it might be futuristic to control your lights via your tablet, every connected device you introduce to your home can be a potential gateway for a criminal.
Check your credit report for any suspicious financial activity
Comments
Be the first to comment
Do you want to comment on this article? You need to be signed in for this feature
